Cross-ministerial Strategic Innovation Promotion Program (SIP) Second Phase: Cyber-Physical Security for IoT Society
This program is being promoted in collaboration with the Japanese Cabinet Office, the Ministry of Internal Affairs and Communications, the Ministry of Economy, Trade and Industry, and NISC. This page provides information on research and development activities, events, and calls for proposals being carried out by NEDO regarding the program.
Research Summary
IoT is a fundamental technology of Society 5.0. IoT devices embedded in physical spaces, such as social infrastructure, industrial systems, and natural environments, create added values and services and bring significant benefits to the economy and society. IoT creates these benefits and values for society by connecting physical spaces to cyberspace through the Cloud via various networks, and it works in collaboration with advanced knowledge processing (represented by AI) and performs analytical processing of big data.
On the other hand, the scope of the targets of cyberattacks is rapidly expanding, and attack techniques are becoming more advanced. The threat of cyberattacks can be found in all industrial activities, not only in cyberspace but also in physical spaces.
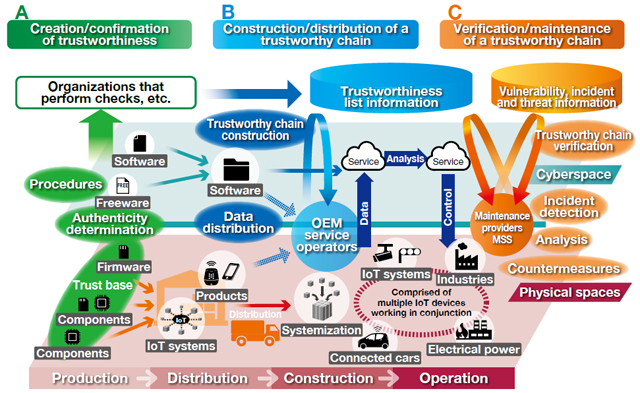
With the spread and expansion of IoT, supply chain risks of illicit programs being added to products and services have manifested, as have risks of modifications to products and services during the manufacturing and transport process. This program aims to enhance an IoT society’s security by establishing a cyber-physical security countermeasure infrastructure that protects entire large-scale supply chains, including small and medium-sized businesses and IoT systems and services. Incorporated into operating supply chains in a practical manner, this infrastructure protects and strengthens an IoT-based society against cyber threats.
Research and development activities
(A) Research and development of technologies for creating/verifying trust
The security of individual IoT devices and services needs to be improved. Research and development activities will be carried out on technology for creating and confirming trustworthiness to ensure the security of various IoT systems and services and an entire supply chain.
(B) Research and development of technologies for constructing and circulating a trustworthy chain
Research and development activities will be carried out on technology to construct a trustworthy chain for IoT systems, services, and supply chains. It will enable information to be distributed in a secure manner and ensure that security is maintained in various social infrastructures and services as well as wide-ranging supply chains.
(C) Research and development of technologies for verifying and maintaining a trustworthy chain
Research and development will be conducted on technologies that make it possible to verify and maintain the safe operation of a trustworthy chain in IoT systems and services and supply chains.
What’s NEW
| October 22nd, 2021 | The online Symposium on SIP/Cyber Physical Security to meet with the requirements for IoT Society |
| November 6th, 2020 | The online Symposium on SIP/Cyber Physical Security to meet with the requirements for IoT Society |
| April 2020 | Link page updated |
| March 2020 | Conference page updated |
| November 2019 | Symposium page updated |
| November 2019 | Cyber-Physical Security for IoT Society page opened |
Symposiums, seminars and business events, and international conferences
- "Cyber Physical Security for IoT Society" ONLINE Symposium 2021
 Keynote speech
Keynote speech (Opening Remarks) How to Bolster the Cyber-Physical System's Supplychain Security
(Opening Remarks) How to Bolster the Cyber-Physical System's Supplychain Security (Plenary Speech) SolarWinds: Observations and Lessons Learned
(Plenary Speech) SolarWinds: Observations and Lessons Learned (Plenary Speech) The landscape of IoT society -from the Connected Car and Mobility viewpoint ?
(Plenary Speech) The landscape of IoT society -from the Connected Car and Mobility viewpoint ?
- Thematic content
- Development of SCU Application Systems leading to Social Implementation(452KB)
- Countermeasure Technologies against Hardware Trojan(282KB)
- Development of Security Assurance Scheme for SCU which can be embedded to low cost IoT devices(234KB)
- Authenticity and integrity monitoring technology for IoT device configuration(829KB)
- Lightweight Monitoring of Program Authenticity and Integrity for IoT Devices in Operation(472KB)
- Continuous Security Protection by Selection Technology for Trustworthy Connection(772KB)
- Secure data distribution environment that supports supply chain and business collaboration in trust(Overview)(865KB)
- Selection Technology for Trustworthy Connection(887KB)
- Trial for Solving Local Government Issues by Selection Technology for Trustworthy Connection(907KB)
- Anomaly Detection for Cyber-Physical Systems(921KB)
- Impact Assessment and Countermeasure Execution Support Technology(961KB)
- Presentation materials(1.3MB)

Japan Pavilion
- Acquisition, Technology & Logistics Agency Symposium 2019 (Japanese)
November 2019
 Pamphlet (1.3MB) (Japanese)
Pamphlet (1.3MB) (Japanese)
Poster booth
- Research and Development Plan for Cyber-Physical Security for IoT Society Symposium 2019 (Japanese)
October 2019
 Pamphlet (5.8MB)
Pamphlet (5.8MB)
Presentation materials
 Lecture by "Efforts to ensure supply chain cybersecurity in Cabinet Secretariat andexpectation for SIP" Tomoo Yamauchi (2.9MB) (Japanese)
Lecture by "Efforts to ensure supply chain cybersecurity in Cabinet Secretariat andexpectation for SIP" Tomoo Yamauchi (2.9MB) (Japanese) Project review (4.0MB) (Japanese)
Project review (4.0MB) (Japanese)
 Lecture hall
|
 Exhibition hall
|
 3rd ENISA - Europol IoT Security Conference
3rd ENISA - Europol IoT Security Conference
October 2019
 Presentation materials (1.6MB)
Presentation materials (1.6MB)
Links
 Cabinet Office: Cross-ministerial Strategic Innovation Promotion Program (SIP) (Japanese)
Cabinet Office: Cross-ministerial Strategic Innovation Promotion Program (SIP) (Japanese)
 NEDO:Cross-ministerial Strategic Innovation Promotion Program (SIP)
NEDO:Cross-ministerial Strategic Innovation Promotion Program (SIP)
Development Results
 Results Report Database (Japanese)
Results Report Database (Japanese)
Inquiries
Internet of Things (IoT) Promotion Department,
New Energy and Industrial Technology Development Organization (NEDO)
E-mail: cyber-sec2@nedo.go.jp
Last Updated : June 27, 2022